Yubikey Two Factor Authentication on Arch Linux

Goals:
Lock the computer and kill any active terminal sessions when the Yubikey is removed
Require Yubikey to be pressed when using
sudo,su.Require the Yubikey for initial system login, and screen unlocking.
Use it to authenticate 1Password.
By 2FA I mean I want to have my Yubikey inserted into the computer, have to press it, and have to enter my user password to use these features.
Autolock on Removal
I followed this guide to accomplish the auto-lock when the key is removed.
Summary:
Insert yubikey
sudo udevadm monitor --environment --udevRemove yubikey
We are looking for
ID_MODEL=sudo nano /etc/udev/rules.d/20-yubikey.rulessudo udevadm control --reload-rules && sudo udevadm triggerpaste in
ACTION=="remove", ENV{ID_MODEL}=="YubiKey_OTP+FIDO+CCID", RUN+="/home/nathan/.config/lockscreen.sh"
nano ~/.config/lockscreen.shpaste in:
#!/usr/bin/sh
# this script is only suitable for a single-use machine as the following will lock and kill all nonroot sessions
# if unable to unlock your screensaver screen lock, check the permissions of your U2F key mappings. Your screen lock
# will run under your current user permission
user=`ps aux | grep -v root | grep session | head -n 1 | awk '{print $1}'`
sessionids=`loginctl list-sessions | grep ${user} | awk '{print $1}'`
for sessionid in $sessionids
do
loginctl lock-session $sessionid
echo "U2F locked sessionid $sessionid ($user)" | systemd-cat -p info -t udev
done
# close any other tty sessions
ttys=`who | grep tty | grep -v \(:0\) | awk '{print $2}'`
for tty in $ttys
do
pkill --signal HUP -t $tty
echo "U2F killed $tty ($user)" | systemd-cat -p info -t udev
done
kill $(ps aux | grep 'konsole' | awk '{print $2}')
sudo chmod 700 ~/.config/lockscreen.shcp ~/.config/lockscreen.sh ~/.config/lockscreen.sh.baknano ~/.config/removeYubilock.shpaste in
#!/bin/bash
rm ~/.config/lockscreen.sh
echo "Remove the YubiKey and press any key to continue"
while [ true ] ; do
read -t 3 -n 1
if [ $? = 0 ] ; then
cp ~/.config/lockscreen.sh.bak ~/.config/lockscreen.sh
echo "Lockscreen file replaced"
exit ;
else
echo "waiting for the keypress"
fi
done
sudo chmod 700 ~/.config/removeYubilock.sh
Warning!
MAKE A BACKUP OF YOUR PAM.D CONFIGS NOW.sudo cp -R /etc/pam.d ~/pam.d.b
Even better, put them on a flash drive with 777 perms.
Should you fail to do so, you could make your system completely locked up. Don't blame me if your whole system is unlockable. Follow this guide to reset the stock pam configs.
If your root partition is encrypted, you might be SOL. I don't know I haven't tried, but think I saw something about it in my googling.
Adding a key to your user
This guide is a reference, for me, and I only have one set of keys, for my user. No one else uses my rig. This guide reflects that need.
Follow the official ArchWiki Only do the "Adding a Key" section.
To summarize:
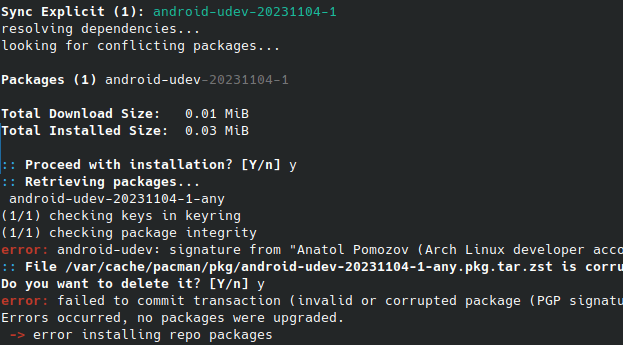
sudo pacman -S pam-u2fmkdir ~/.config/Yubicopamu2fcfg -o pam://hostname -i pam://hostname > ~/.config/Yubico/u2f_keys
Add entries to the pam.d files
Move into the pam.d directorycd /etc/pam.d
Use sudo nano to edit the following files.
For each of these, add this line to the top of the fileauth required pam_u2f.so cue [cue_prompt=Yubikey required for authentication.]
to "login" for normal shell logins.
to "polkit-1" for system prompts.
to "sudo" for sudo..
to "su" for su...
For each of these, add them under the auth include system-login" lines.
to "kde" for first plasma login.
to "sddm" for plasma unlocks.
Reboot
Notes for use:
Startup will hang if you start the system with the key installed.
When authenticating, you have to press the Yubikey first (it flashes), then enter your password
if your home partition is encrypted, you won't be able to login on reboots.
I haven't figured out how to make gnome-keyring respect the logins yet. Definitely a pam issue, but I'll update this guide when I figure it out.
As stated in the ArchWiki,
"This method will not work with encrypted home partitions because the decryption is not done before the login process is completed, so the u2f_keys file is unavailable. In this case, use a central mapping file as explained in the official documentation of pam-u2f."